Looks like the crypto criminals have not had enough. The non-profit organization, Make-A-Wish, that makes critically ill children’s wishes come true, joins the league of websites infected by bitcoin scams.
Could they stoop any low? The holiday season is just around the corner, and these crypto criminals targeted a charity based organization.
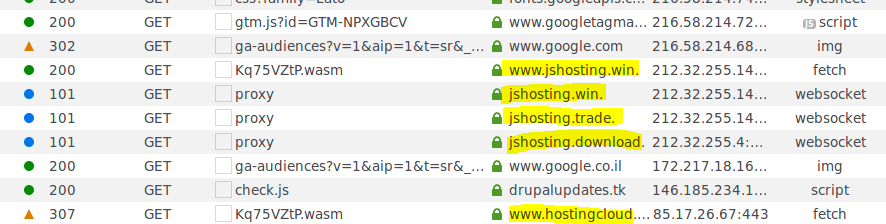
According to Trustwave Holdings, Make-A-Wish organization’s official site was embedded with a script that allowed these scammers to mine the visitors’ cryptocurrency. Delving in deeper, it was found that the ”drupalupdates.tk” was used to host the mining script. Rings any bell? Yes, it is the same domain that affected hundreds of Drupal websites. An update in May did tackle the issue, but those who did not make use of the update became vulnerable to hacking. Unfortunately, Make-A-Wish too failed to comply, hence the loss.
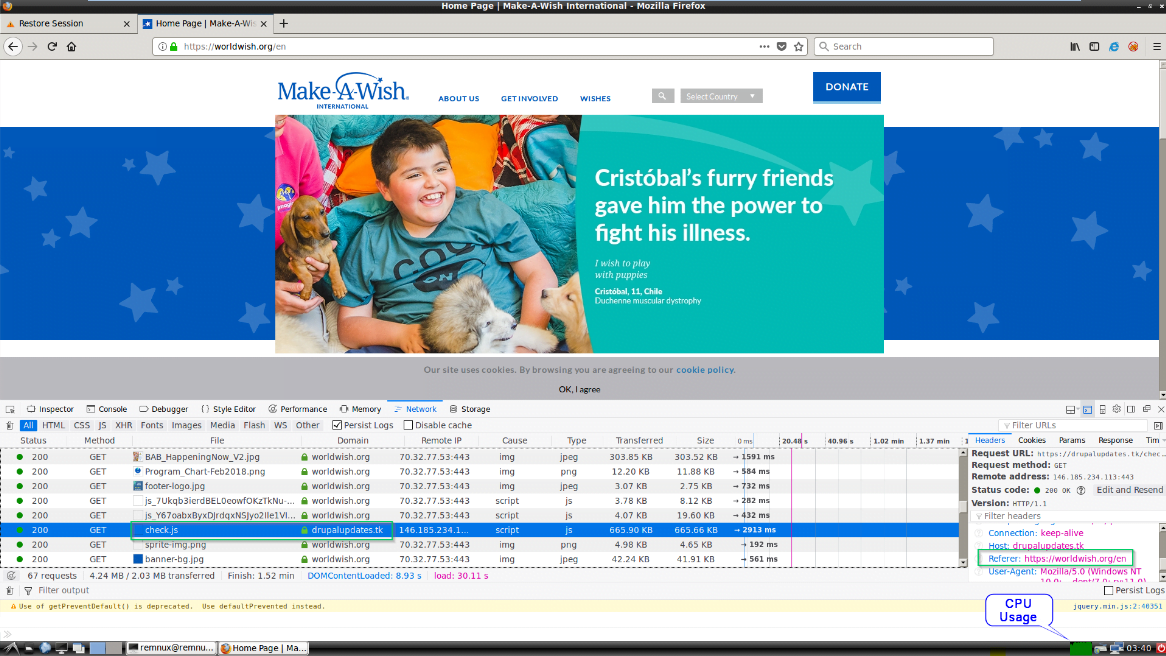
Well, these cybercriminals tried to outsmart the system by using different domain names (hosting the JavaScript miner). Fortunately, the Trustwave SWG was intelligent enough to identify it.
Luckily, the organization did not lose anything because of it. The patch was removed after some time and the site is safe now. However, for the people who have visited the site at the time when the patch was there, their CPU got overtaxed.
Previously Target and Google G Suite got their Twitter accounts infiltrated with the same bitcoin scam. These crypto criminals are literally the human version of the idiom ‘Go hard or go home.’ They went even further by creating a fake Elon Musk profile to spread the bitcoin scam using his name.
As the holiday season approaches, the number of attempts of cryptojacking have risen to an alarming rate. These crypto criminals are not going to stop trying their luck until they hit the jackpot (or maybe they are not going to stop at all).
Just a few days ago, RiskIQ released a report featuring the blacklisted sites and apps for this year’s Black Friday sale. The popularity of the year’s much awaited Black Friday sale is growing at an exponential rate and so is the greed of the cybercriminals.
Trustwave Holdings mentioned a few mitigations that included:
- A sound endpoint protection
- Keeping websites updated
- Setting up WAF to protect the website
- Keeping an eye on even the slightest changes on the website
So, make sure your site is safe because cryptojacking is in the air.
Do let us know what you think in the comments section below!






Looks like they can stoop lower 🙁
Saw this. https://support.google.com/mail/thread/97622912?hl=en
Scum