On January 9th, 2009, Satoshi Nakamoto released version 0.1 of what would become the first mainstream cryptocurrency, Bitcoin. Unfortunately, Satoshi Nakamoto is only a pseudonym used by the creator of Bitcoin, so his real identity remains a mystery. What doesn’t remain a mystery, however, is his legacy.
Since the inception of Bitcoin, cryptocurrency and the systems built around it have only grown in popularity. That brings us to today—an age where cryptocurrency is a semi-viable way of making money, however volatile.
But of course, like with anything tech-related, there are risks to investing in cryptocurrencies. Volatility defines Bitcoin, Ethereum, and other cryptocurrencies. Investing also opens people up to losing all of their money through bad investments.
But the number one risk in the cryptocurrency market is security. Due to cryptocurrency trading and investing still being a “niche” industry, not many security standards are put in place, both for cryptocurrencies themselves and the software built around them.
So, with that said, what security risks actually threaten investors and traders? Below are just a few of the risks that investors and traders face when working with cryptocurrency.
3 Risks Facing the Cryptocurrency Market in 2020

1. Cases of Crypto-Fraud
In April, the FBI issued a warning regarding the rise of cryptocurrency scams. The rise in scams are linked to the current COVID-19 pandemic, the logic being that scammers are taking advantage of the fear and hysteria gripping countries.
But the FBI is right: cryptocurrency scams are on the rise, and many people have been tricked. These scams—also called crypto-fraud—take the form of “start-ups” or “fledgling software.”
For example, if someone says they have a new ICO coming up and want you to pitch in, it’s a scam. If someone offers you a large amount of money for your investment, it’s a scam.
These scams also take other forms. Earlier this year, Twitter faced a large hack that had many verified accounts advertising a crypt-wallet, asking followers to donate their money to the wallet linked. This, of course, was a scam.
2. Rise in Malware Attacks
While businesses and developers grow smarter in the field of cybersecurity, so do their rivals, hackers and scammers, and vice versa. It’s impossible to stay ahead; most developers are forced to play catch-up on security.
Unfortunately, the cryptocurrency industry is no different. Malware attacks are a popular way to achieve financial gain amongst hackers. There are various ways they accomplish malware attacks. Some hackers hide malware in inconspicuous websites. Others spread malware from device to device through public networks.
There are tons of ways hackers accomplish malware attacks, not all of them obvious to even experts.
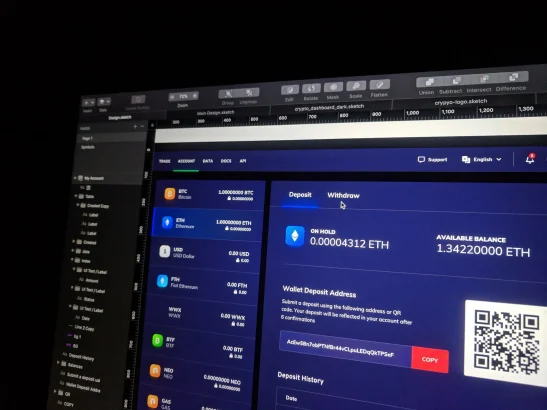
3. Disreputable Trading Platforms
What use would cryptocurrency be if there weren’t places to trade them? To exchange and sell them? There wouldn’t be any, which is why there are dozens of cryptocurrency trading platforms. Unfortunately, not all of these carry great reputations.
Studies show that many cryptocurrency trading platforms don’t practice proper security, putting their users at risk of fraud. Fortunately, there are secure trading platforms, but it’s up to the user to find these.
4 Ways to Stay Protected While Trading Cryptocurrency
It’s clear that security lacks the cryptocurrency industry, but that doesn’t mean users can’t protect themselves. Here are just a few ways you can invest and trade cryptocurrency without becoming a victim of fraud, malware, and vice versa.
1. Use a VPN

To the common person, public networks offer a convenient way to connect to the Internet. To cybercriminals, however, public networks represent something far more sinister. To them, public networks offer a way to spread malware to multiple people, putting their information at risk.
For users that routinely take advantage of public networks, there are a few ways they can protect themselves, one of them being a VPN. A VPN, short for Virtual Private Network, encrypts a user’s data and hides their activity from other people on a network, making it near impossible for a cybercriminal to intercept their data or target them.
A VPN can be downloaded in a few simple steps and offers unlimited security. I highly recommend one for daily use, especially if you use public networks often.
2. Use a Multi-Signature Address

Two-factor authentication has vastly improved the security of accounts everywhere. Without it, cybercriminals would easily access accounts without any sort of verification (besides passwords) like in the early days of the Internet.
Fortunately for cryptocurrency investors, some crypto-wallets allow a form of two-factor authentication called multi-signature authentication.
Multi-signature addresses are used in wallets that require multiple authentications before a transaction is processed. This is vital for protecting your wallet from cybercriminals.
3. Educate Yourself on Common Scams/Fraud Attempts

Installing the latest security software, keeping up-to-date with the latest cybersecurity news, picking the best cryptocurrency: all of this doesn’t matter if you don’t actually know what you’re protecting yourself against.
Taking some time out of your day to familiarize yourself with the current threats haunting the crypto world will better equip you to deal with those threats. Then, you’ll focus on the major threats during that time instead of staying unaware.
4. Subscribe to a Secure Email Service
Crypto-frauds take on all shapes and forms. You may get a call from “Microsoft” that pledges to fix your “computer issues” in exchange for a small cryptocurrency payment to a certain address. You may find a website that tries to scam you by saying your computer is locked and, to unlock it, requires a payment to unlock it.
These are fake, obviously, but trick a lot of people. Many of these crypto-scams come through email, and to avoid getting these, think about securing to secure email service. Email services are built from the ground up to be secure, scanning through email and deciphering whether an email comes from a trusted source and contains legitimate content.





Share Your Thoughts