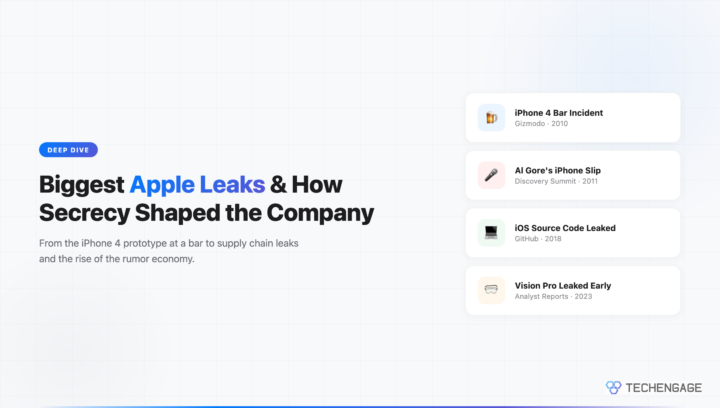
In September 2011, former Vice President Al Gore accidentally confirmed that Apple would release multiple new iPhones the following month. Speaking at the Discovery Invest Leadership Summit in Johannesburg, he casually referred to “the new iPhones” coming in October. For Apple, a company that had built its entire product launch strategy around secrecy and surprise, having a board member spoil the reveal was a nightmare scenario.
That slip became one of many entries in a long history of Apple leaks that executives at Cupertino would rather forget. From lost prototypes in bars to iOS source code appearing on GitHub, Apple has fought a constant battle to keep its products under wraps. That battle has shaped how the company operates, how it treats employees, and how the entire tech industry thinks about product launches.
Steve Jobs and the Architecture of Secrecy
Steve Jobs didn’t just prefer secrecy. He treated it as a competitive weapon. Apple’s product launches under Jobs were theatrical events designed to create maximum surprise and emotional impact. The black cloth draped over an unrevealed product, the calculated pauses, the phrase “one more thing” — all of it depended on nobody knowing what was coming. Jobs understood that anticipation built through secrecy generated far more press coverage and consumer excitement than any marketing campaign could achieve.
Inside Apple, this translated into a compartmentalized culture where most employees had no idea what other teams were building. Engineers working on the original iPhone were reportedly told they were developing a tablet. Teams operated under code names, and access to information was granted strictly on a need-to-know basis. Employees who violated these protocols faced immediate termination. Jobs personally called at least one journalist to express fury over leaked information, and Apple’s legal department sent cease-and-desist letters to rumor sites with a regularity that bordered on obsessive.
This approach worked spectacularly during Apple’s most transformative era. The iPod, the iPhone, and the iPad were all revealed to a genuinely shocked public, and the resulting media frenzy was worth billions in free publicity. But maintaining that level of secrecy across a company that would grow to employ over 160,000 people proved increasingly difficult.
The iPhone 4 Prototype: A Bar, a Lost Phone, and a Legal Battle
The most infamous Apple leak happened on a spring evening in 2010. Gray Powell, a young Apple engineer, was celebrating his 27th birthday at Gourmet Haus Staudt, a German beer garden in Redwood City, California. He left his phone on a bar stool. What looked like an iPhone 3GS in a disguised case was actually a prototype of the unreleased iPhone 4, complete with its radical new flat-edged design, front-facing camera, and higher resolution display.
The phone ended up in the hands of Brian Hogan, who sold it to Gizmodo for $5,000. Gizmodo editor Jason Chen published a detailed teardown on April 19, 2010, confirming the device’s authenticity and revealing the iPhone 4’s design months before Apple’s official announcement. The story generated millions of pageviews and dominated tech news for weeks.
Apple’s response was swift and aggressive. Jobs personally called Gizmodo’s parent company, Gawker Media, demanding the phone’s return. When that didn’t produce immediate results, Apple involved law enforcement. The Rapid Enforcement Allied Computer Team (REACT), a California task force, obtained a warrant and raided Jason Chen’s home, seizing computers and hard drives. Legal scholars debated whether the raid violated journalist shield laws, and the case became a flashpoint in discussions about press freedom in the digital age. The San Mateo County District Attorney ultimately charged Hogan with misappropriation of lost property. The charges against him were eventually dropped.
The incident revealed just how far Apple would go to protect its secrets. It also demonstrated a painful truth: no amount of internal security can prevent a simple human mistake from undermining months of careful secrecy.
Al Gore’s iPhone Slip and the Board Member Problem
Al Gore joined Apple’s board of directors in 2003. By 2011, he had been a board member for eight years and was presumably well-versed in Apple’s confidentiality expectations. That made his September 2011 slip all the more remarkable. Speaking to an audience at the Discovery Invest Leadership Summit in South Africa, Gore casually mentioned that “the new iPhones” would be released the following month.
At the time, Apple had not confirmed the existence of any new iPhone, let alone multiple models. The use of “iPhones” in the plural suggested either that Apple was planning to release more than one model or that multiple units of a single new model would be available — which was obvious enough that the phrasing only made sense as a hint at multiple products. The tech press seized on the statement as confirmation that Apple was planning both the iPhone 4S and possibly a lower-cost model.
Apple’s board members have always existed in a peculiar position regarding the company’s secrecy culture. They have access to the company’s most sensitive strategic plans but operate in public-facing roles where casual remarks carry enormous weight. Gore’s slip was embarrassing but ultimately inconsequential to iPhone sales. However, it highlighted a vulnerability in Apple’s information security that no amount of employee surveillance could address: the people at the very top of the organization were the hardest to control.
The iOS Source Code Leak of 2018
In February 2018, someone posted what appeared to be a significant portion of iBoot source code on GitHub. iBoot is the program responsible for booting iOS devices — essentially the first thing that runs when you turn on an iPhone. It is one of the most security-critical components in Apple’s entire software stack, and having its source code publicly available was a potential goldmine for security researchers and hackers alike.
The leaked code was from iOS 9, which was already two major versions old at the time. Apple quickly issued a DMCA takedown notice to GitHub, confirming the code’s authenticity in the process. The company stated that the security of its products did not depend on source code secrecy, pointing to the multiple layers of hardware and software protection built into iOS devices.
Investigations traced the leak to a low-level Apple employee who had shared the code with friends, who then shared it further until it reached the jailbreaking community and eventually GitHub. The incident underscored a reality that every large technology company faces: with tens of thousands of employees, preventing all unauthorized disclosures is essentially impossible. The best a company can do is limit the blast radius by compartmentalizing access and detecting leaks quickly.
Apple’s Internal Security Machine
Apple operates an internal team commonly referred to as the “New Product Security” (NPS) team, though its exact name and structure have varied over the years. This group functions as something between corporate security and internal affairs. Their job is to prevent leaks, investigate suspected leakers, and maintain the information barriers between different product groups within the company.
Reports from former employees describe an environment where NPS conducts surprise audits, monitors internal communications, and interviews employees suspected of sharing information outside approved channels. New hires working on sensitive projects reportedly sign additional NDAs beyond the standard employment agreement. Some teams work in windowless rooms with security cameras, and prototypes are tethered to desks with cable locks.
Apple has also filed lawsuits against leakers and the publications that report on leaked information. In 2004, the company sued several John Doe defendants and the operators of Apple Insider and PowerPage for publishing details about an unreleased product called “Asteroid.” The case went to the California Court of Appeal, which ruled in 2006 that online journalists were entitled to the same legal protections as traditional reporters — a landmark decision that Apple lost.
Despite these efforts, Apple’s leak problem has grown worse over time, not better. The company’s expanding global supply chain has created thousands of potential leak points that no internal security team can fully monitor.
Supply Chain Leaks: The Foxconn Factor
The most consistent source of Apple product leaks over the past decade has not been Cupertino employees but the sprawling manufacturing network in China. Foxconn, the primary assembler of iPhones, employs hundreds of thousands of workers across its facilities. Case manufacturers, screen suppliers, and component vendors all receive specifications months before a product launches. Each of these companies represents a potential leak source.
Leaked iPhone case designs became so common by the early 2010s that accessory manufacturers began producing cases for unreleased iPhones based on leaked schematics, timing their inventory to arrive the same week as Apple’s launch. CAD drawings of new iPhone dimensions would appear on Chinese social media months in advance, giving the entire accessory ecosystem a head start that Apple could not prevent without fundamentally changing how it manufactured products.
Apple has responded by working with Chinese authorities to investigate and prosecute supply chain leakers, reportedly stationing its own security personnel at supplier facilities, and designing products with deceptive specifications during early production runs to identify which supplier leaked information. Despite all of these countermeasures, supply chain leaks remain Apple’s single largest source of pre-launch information reaching the public.
The Leak Economy: Analysts, Journalists, and Rumor Sites
Apple leaks created an entire ecosystem of publications, analysts, and social media accounts dedicated to predicting what the company would announce next. This leak economy became a significant force in tech media and financial markets.
Ming-Chi Kuo, an analyst at TF International Securities, built his reputation almost entirely on the accuracy of his Apple supply chain predictions. By cultivating sources within Apple’s Asian supplier network, Kuo consistently predicted iPhone features, pricing, and production timelines months in advance. His research notes moved Apple’s stock price, and his predictions were treated as near-certain by the tech press.
Mark Gurman, now at Bloomberg, became arguably the most influential Apple reporter in the world by developing sources inside Apple itself. His reporting consistently revealed product plans, internal organizational changes, and software features before Apple’s official announcements. Gurman’s coverage became so reliable that some observers joked he was Apple’s unofficial communications channel — a way for the company to manage expectations and test public reaction to upcoming products without committing to an official announcement.
Rumor sites like 9to5Mac and MacRumors evolved from hobbyist forums into major media properties driven largely by leaked information. These sites developed sophisticated networks of tipsters, learned to evaluate the reliability of different leak sources, and built audiences of millions who checked daily for the latest Apple rumors. The irony is that Apple’s culture of secrecy made leaked information more valuable, not less. If Apple freely discussed upcoming products, the leak economy would collapse overnight.
Tim Cook’s Apple: A Different Approach to Leaks
When Tim Cook took over as CEO in 2011, he inherited Jobs’ secrecy culture but brought a different management philosophy. Cook came from operations and supply chain management, and he understood that some information sharing was necessary to run an efficient global manufacturing operation. He also faced a practical reality: Apple had grown far too large and too dependent on external partners to maintain the level of secrecy that Jobs demanded.
Cook publicly warned leakers in at least one internal memo that leaked to the press — an irony not lost on commentators. He reportedly told employees that Apple would pursue leakers aggressively and that people who leaked confidential information “do not belong here.” But actions mattered more than words, and the volume of Apple leaks continued to increase throughout Cook’s tenure.
Under Cook, Apple has also shifted partially away from the surprise launch model. The company now pre-announces some features and products, particularly software updates at its annual Worldwide Developers Conference. Apple Intelligence, the company’s AI initiative announced at WWDC 2024, was previewed months before its gradual rollout — a deliberate strategy to manage expectations for a technology that Cook knew would face scrutiny. The Vision Pro headset was announced in June 2023, a full seven months before it went on sale, partly because so much had already leaked that a surprise reveal was impossible.
Vision Pro and the End of the Surprise Era
Apple Vision Pro became perhaps the most thoroughly leaked product in Apple’s history. By the time Tim Cook held up the headset on stage at WWDC 2023, analysts and journalists had already published its approximate price point, display specifications, external battery design, and general form factor. Bloomberg’s Gurman had reported on the project, codenamed N301, for years before the official announcement.
The Vision Pro’s leak trajectory illustrated how the modern information landscape has made Apple-style secrecy nearly impossible for major hardware products. A device with that many components, sourced from that many suppliers, assembled by that many workers, simply cannot remain secret through years of development. Apple reportedly delayed the device multiple times, extending the window during which leaked information could accumulate.
By 2026, the pattern for major Apple launches has settled into a predictable rhythm. Analysts publish supply chain intelligence 6-12 months before an announcement. Bloomberg and other outlets report on internal development progress. Leaked CAD files and case designs confirm the physical form factor. By the time Apple takes the stage, the audience already knows roughly 80% of what will be shown. The remaining 20% — usually pricing, specific software features, and availability dates — provides whatever surprise is left.
Does Apple’s Secrecy Culture Still Work?
The honest answer is that Apple’s secrecy culture works differently than it once did, and the company has adapted accordingly. The era of genuinely shocking product reveals ended sometime around 2015, when supply chain leaks became so comprehensive that major hardware surprises became nearly impossible. What Apple has preserved is secrecy around software innovations, pricing strategy, and the specific ways hardware and software integrate — areas where the supply chain cannot provide advance intelligence.
Apple’s secrecy also still serves important competitive functions beyond launch theatrics. Keeping product roadmaps confidential prevents competitors from preemptively copying features. Maintaining information barriers between teams reduces the risk of coordinated leaks. The culture of secrecy, even if imperfect, creates a baseline expectation of discretion that probably prevents far more leaks than would occur in a more open corporate culture.
The biggest change is philosophical. Jobs treated leaks as personal betrayals and existential threats to Apple’s brand. Cook treats them as operational challenges to be managed and mitigated. Neither approach can prevent leaks entirely, but Cook’s pragmatic stance has allowed Apple to maintain its competitive edge while acknowledging that the information environment of 2026 is fundamentally different from 2007. The surprise is no longer the product itself. The surprise is in how well it works when you finally hold it in your hands.
Frequently Asked Questions
What happened with the iPhone 4 prototype left at a bar?
In 2010, Apple engineer Gray Powell accidentally left an iPhone 4 prototype at a bar in Redwood City, California. It ended up being sold to Gizmodo for $5,000, which published a full teardown revealing the unreleased design. Apple involved law enforcement, resulting in a police raid on the journalist’s home and criminal charges against the finder.
How did Al Gore leak iPhone information?
At the Discovery Invest Leadership Summit in Johannesburg in September 2011, Apple board member Al Gore casually referenced upcoming iPhones using the plural form, confirming that Apple was planning to release new iPhone models the following month before the company had made any official announcement.
How does Apple enforce its secrecy internally?
Apple operates an internal security team that conducts surprise audits, monitors communications, and investigates suspected leakers. Employees on sensitive projects sign additional NDAs, work in secured rooms with cameras, and have prototypes tethered to desks. Violations can result in immediate termination, and Apple has filed lawsuits against both leakers and publications.
Why do most Apple leaks come from the supply chain?
Apple’s manufacturing partners in China, including Foxconn and various component suppliers, employ hundreds of thousands of workers who handle product specifications months before launch. The sheer number of people involved makes preventing all leaks impossible. Case manufacturers and component suppliers routinely leak dimensions, features, and designs.
Can Apple still do surprise product launches?
Major hardware surprises have become nearly impossible due to supply chain leaks and analyst reporting. By the time Apple announces a new product, roughly 80% of its specifications are already public knowledge. Apple has adapted by pre-announcing some products and focusing surprise elements on software features, pricing, and integration details that supply chains cannot reveal.
Who is Mark Gurman and why is he significant to Apple leaks?
Mark Gurman is a Bloomberg journalist who has become the most influential Apple reporter by developing deep sources inside the company. His reporting consistently reveals product plans, organizational changes, and software features before official announcements. His coverage is so reliable that many consider him Apple’s unofficial communications channel.





Mr. Eco-man has three 30″ Cinema Displays fired up. He’s a blowhard and a fraud.