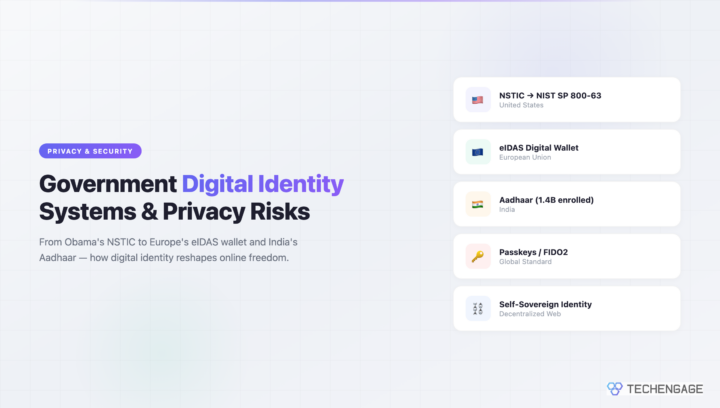
In January 2011, the Obama administration announced the National Strategy for Trusted Identities in Cyberspace (NSTIC), a plan to create a standardized digital identity ecosystem for online transactions. Critics immediately compared it to a “national internet ID card” and warned about single points of failure, government surveillance, and the erosion of online anonymity. Supporters argued that the fragmented state of online authentication was itself a security disaster and that some standardization was inevitable.
Fifteen years later, the debate those critics and supporters were having has played out across the entire world. Every major government has either built or is building a digital identity system. The European Union mandates digital identity wallets for all citizens by 2026. India enrolled 1.4 billion people in Aadhaar, the largest biometric database in human history. China tied internet access to real-name registration. The privacy concerns raised in 2011 were not paranoid speculation. They were accurate predictions of exactly the tensions that define digital identity today.
Obama’s NSTIC: What Was Actually Proposed
The National Strategy for Trusted Identities in Cyberspace was released as a draft in June 2010 and finalized in April 2011. Despite the alarming name, NSTIC was not a proposal for a government-issued internet ID card. The strategy outlined a vision for a private-sector-led “identity ecosystem” where multiple identity providers would compete to offer secure authentication services. The government’s role would be limited to setting standards and coordinating adoption.
The core idea was straightforward: instead of managing hundreds of passwords across different websites, consumers could authenticate through a trusted identity provider — similar to how a driver’s license verifies your identity in person. The Commerce Department, not the NSA or DHS, was designated to lead the initiative, a deliberate choice to frame it as an economic rather than security project.
Privacy advocates raised three fundamental objections. First, any centralized authentication system creates a single point of failure — compromise one identity provider and you compromise everything connected to it. Second, even with private-sector providers, the government would inevitably gain access to authentication data through legal processes or intelligence programs. Third, the system would create a comprehensive record of every online transaction tied to a verified real-world identity, effectively ending online anonymity for participants.
These objections were prescient. Every government digital identity system built since NSTIC has faced exactly these challenges, and none has fully resolved them.
What Happened to NSTIC
NSTIC itself never became the universal internet ID that critics feared. The initiative funded several pilot programs through the National Institute of Standards and Technology (NIST), testing federated identity systems in healthcare, education, and government services. These pilots produced useful technical insights but never achieved mainstream adoption.
The lasting legacy of NSTIC is NIST Special Publication 800-63, the Digital Identity Guidelines. This document became the de facto standard for digital authentication across U.S. government agencies and heavily influenced private-sector practices. SP 800-63 introduced the concept of identity assurance levels (IALs) and authenticator assurance levels (AALs), creating a framework for matching authentication strength to the sensitivity of the transaction. Its most recent revision, published in 2024, incorporates guidance on phishing-resistant authentication, biometrics, and passkeys.
The marketplace that NSTIC envisioned — multiple competing identity providers offering standardized authentication — did materialize, just not in the form the government planned. It came through Silicon Valley.
Federated Login: How Big Tech Built What Government Couldn’t
While NSTIC was running pilot programs, Google, Facebook, and Apple were building exactly the kind of identity ecosystem the strategy described — except controlled by corporations rather than governed by public standards. “Sign in with Google” launched in 2010. Facebook Login became ubiquitous across the web. Apple introduced “Sign in with Apple” in 2019, differentiating itself with privacy features like email relay and minimal data sharing.
By 2026, these three companies collectively serve as identity providers for billions of online accounts. If you have ever used “Continue with Google” to create an account on a new service, you have participated in a federated identity system that operates almost exactly as NSTIC envisioned — except with no government oversight, no standardized privacy protections, and no democratic accountability.
The NSTIC critics who warned about single points of failure were proven right, but the single points turned out to be corporate rather than governmental. A compromised Google account now threatens not just email but every service authenticated through Google’s identity system. The 2011 debate about government surveillance became somewhat moot when it turned out that corporations were collecting far more personal data than any government system had proposed.
Europe’s eIDAS and the Digital Identity Wallet
The European Union took the most ambitious approach to government digital identity with the eIDAS regulation. The original eIDAS, adopted in 2014, established a framework for cross-border recognition of electronic identification between EU member states. The revised eIDAS 2.0, which entered into force in 2024, goes much further: it mandates that every EU member state offer a European Digital Identity Wallet to all citizens by 2026.
The EU Digital Identity Wallet is designed to let citizens store and present identity credentials, driving licenses, diplomas, bank account details, and other documents from their smartphone. The wallet would work across all EU member states and be accepted by both government services and private-sector companies above a certain size. Major platforms like Amazon, Google, and Meta would be required to support wallet authentication.
The privacy implications are significant. The wallet is designed with selective disclosure — you could prove you are over 18 without revealing your exact birthdate, or prove you hold a valid credential without revealing which institution issued it. These privacy-by-design features address some of the concerns raised about NSTIC. However, critics point out that the underlying infrastructure still creates a centralized record of when and where citizens authenticate, and that government access to this data through legal processes remains a fundamental concern.
India’s Aadhaar: The World’s Largest Biometric Database
India’s Aadhaar system, launched in 2009, enrolled over 1.4 billion people by assigning each a unique 12-digit identification number linked to biometric data including fingerprints and iris scans. It is the largest biometric identification system ever built, and its scale makes it one of the most consequential digital identity experiments in human history.
Aadhaar’s proponents credit it with transforming government service delivery. Direct benefit transfers using Aadhaar authentication reportedly reduced fraud by billions of dollars annually. Financial inclusion increased dramatically as Aadhaar-linked bank accounts gave hundreds of millions of previously unbanked citizens access to the formal financial system. The system’s authentication API allows private businesses to verify customer identity instantly, enabling digital services in regions where traditional identification infrastructure was nonexistent.
The privacy controversies have been equally dramatic. In 2018, India’s Supreme Court ruled in the landmark Puttaswamy case that Aadhaar was constitutional but imposed significant restrictions. The court prohibited private companies from requiring Aadhaar for services, limited the government’s use of the system to specific welfare programs, and struck down the provision allowing phone companies to require Aadhaar verification. The ruling affirmed privacy as a fundamental right under the Indian constitution.
Despite the court’s restrictions, Aadhaar data breaches have been documented multiple times. Reporters and security researchers demonstrated that the centralized database was accessible through unauthorized channels, and the personal data of millions of citizens was exposed. These incidents validated the single-point-of-failure argument that critics have made against every centralized identity system since NSTIC.
China’s Real-Name Internet and Social Credit
China represents the extreme end of government digital identity — the scenario that Western privacy advocates feared most when NSTIC was proposed. China requires real-name registration for all internet services, including social media, gaming platforms, and messaging apps. Users must verify their identity using their national ID number, and this verification links their online activity directly to their real-world identity.
The social credit system, which has been piloted in various forms across Chinese cities, uses this identity infrastructure to score citizens based on their behavior. While the system is less monolithic than Western media often portrays — it operates as a patchwork of local programs rather than a single national score — the underlying principle is clear: digital identity verification enables behavioral monitoring at scale.
China’s system demonstrates the ultimate trajectory that NSTIC critics warned about. When a government can link every online action to a verified identity, and when that government has the will and infrastructure to analyze that data at scale, the result is a surveillance apparatus that would have been impossible in the pre-digital era.
Passkeys: The Post-Password Future
While governments debated national ID systems, the technology industry pursued a different approach to the authentication problem: eliminating passwords entirely. Passkeys, based on the FIDO2/WebAuthn standard, allow users to authenticate using biometrics (fingerprint or face recognition) or device PINs instead of passwords. The cryptographic key never leaves the user’s device, making phishing attacks fundamentally impossible.
Apple, Google, and Microsoft all began supporting passkeys across their platforms in 2022-2023. By 2026, passkey adoption has reached critical mass for consumer services, with major platforms reporting that passkey-authenticated sessions have significantly higher security than password-based sessions. Google reported that passkey authentication is 40% faster than passwords and has reduced account compromise rates dramatically for users who adopt them.
Passkeys solve the authentication problem without creating the centralized identity infrastructure that NSTIC proposed. Each passkey is unique to a specific website and device, creating no cross-site identity linkage. There is no central database to breach, no single point of failure, and no government-accessible authentication log. In many ways, passkeys represent the privacy-preserving alternative that NSTIC’s critics wished the government had pursued instead.
Self-Sovereign Identity and the Blockchain Experiment
The Web3 movement proposed an even more radical alternative: self-sovereign identity (SSI), where individuals control their own identity credentials without relying on any central authority. Using blockchain technology and decentralized identifiers (DIDs), SSI systems allow users to hold verifiable credentials in a digital wallet they fully control. No government, corporation, or platform can revoke access or monitor usage.
The World Wide Web Consortium (W3C) published the Decentralized Identifiers specification as a recommendation in 2022. Microsoft’s ION project, built on the Bitcoin blockchain, demonstrated that decentralized identity was technically feasible at scale. Several European governments explored DID-based approaches as part of their eIDAS 2.0 implementations.
In practice, self-sovereign identity has struggled to achieve mainstream adoption. The technology is complex, recovery from lost credentials is difficult, and the user experience remains far inferior to “Sign in with Google.” Most consumers, given the choice between privacy-preserving complexity and convenient corporate authentication, have consistently chosen convenience. SSI remains a promising technology looking for a viable path to mass adoption.
Biometric Privacy and the AI Challenge
Biometric authentication, which underpins systems from Aadhaar to iPhone Face ID, faces a growing legal and technological challenge. Illinois’ Biometric Information Privacy Act (BIPA), passed in 2008, became the model for biometric privacy legislation worldwide. BIPA requires informed consent before collecting biometric data and provides individuals with a private right of action — meaning they can sue companies that violate the law without relying on government enforcement.
BIPA litigation has resulted in massive settlements. Facebook paid $650 million in 2021 to settle a class-action lawsuit over its facial recognition feature. Google, Amazon, and TikTok have all faced BIPA lawsuits. The GDPR’s Article 9 provides similar protections in Europe, classifying biometric data as a “special category” requiring explicit consent.
AI deepfakes have introduced a new dimension to identity verification. As synthetic media becomes increasingly convincing, verifying that a person is who they claim to be during remote authentication has become significantly harder. Liveness detection systems — which attempt to distinguish a real face from a photograph, video, or deepfake — are engaged in a continuous arms race with AI generation technology. By 2026, this arms race shows no signs of being won by either side, raising fundamental questions about the long-term viability of biometric remote authentication.
The State of Digital Identity in 2026
The digital identity landscape in 2026 looks nothing like what the Obama administration envisioned in 2011, yet the fundamental tensions are identical. The tradeoff between convenience and privacy, between security and freedom, between government oversight and corporate control — none of these have been resolved. They have simply been distributed across different systems in different countries.
The United States still lacks a national digital identity system. Americans authenticate through a patchwork of corporate providers, government portals with varying levels of security, and an increasingly outdated Social Security number that was never designed to be an identity credential. The NIST guidelines provide technical standards but no mandate for adoption. Login.gov, the federal government’s authentication service, serves several dozen agencies but remains far from universal.
What has become clear since 2011 is that digital identity is not a problem that can be solved once. It is an ongoing negotiation between individuals, corporations, and governments about who gets to verify whom, what data is collected in the process, and who has access to the resulting records. The NSTIC critics were right that any digital identity system carries inherent risks. They were wrong in assuming that refusing to build a system would preserve the status quo. The system got built anyway — just by corporations instead of governments, with less transparency and less democratic accountability than even NSTIC proposed.
Frequently Asked Questions
What happened to Obama’s National Internet ID (NSTIC)?
NSTIC never became the universal internet ID that critics feared. It funded pilot programs through NIST and evolved into the Digital Identity Guidelines (SP 800-63), which became the standard for federal digital authentication. The federated identity marketplace it envisioned was ultimately built by Google, Apple, and Facebook instead.
What is the EU Digital Identity Wallet?
Under the revised eIDAS 2.0 regulation, every EU member state must offer citizens a digital identity wallet by 2026. The wallet stores identity credentials, licenses, and documents on smartphones, with selective disclosure features that let users prove specific claims without revealing unnecessary personal data.
Is India’s Aadhaar system safe for privacy?
Aadhaar has faced significant privacy concerns. India’s Supreme Court upheld it as constitutional in 2018 but imposed restrictions on private-sector use. Multiple data breaches have been documented, exposing personal information of millions. The system demonstrates both the benefits of universal digital identity and the risks of centralized biometric databases.
Will passkeys replace passwords?
Passkeys based on the FIDO2/WebAuthn standard are rapidly replacing passwords for consumer services. Apple, Google, and Microsoft all support passkeys, and adoption reached critical mass by 2026. Unlike passwords, passkeys cannot be phished, reused, or stolen from server breaches, making them fundamentally more secure.
What is self-sovereign identity?
Self-sovereign identity (SSI) uses blockchain and decentralized identifiers to let individuals control their own identity credentials without relying on any central authority. While technically promising, SSI has struggled with mainstream adoption due to complexity, difficult credential recovery, and user experience that lags behind corporate alternatives like Sign in with Google.
How are AI deepfakes affecting identity verification?
AI-generated deepfakes make remote identity verification increasingly difficult. Liveness detection systems that distinguish real faces from synthetic media are in a continuous arms race with improving AI generation technology. By 2026, this challenge has raised fundamental questions about the long-term reliability of biometric remote authentication.





Good, thoughtful points about the very real risks … and yet, the benefits of a secure online identity are real, too, so we need to do something to make that secure identity feasible for all. We already know that most people simply will *not* maintain their security in the current environment, and maintaining (or raising) fear levels will shut more people out of the online world. (And, as a side issue, ponder which people will self-select out and how that discriminatory result affects our cultures both on and off line.)
It feels to me like a common government policing role, and so it comes with the normal government over-reach/misuse risks, and should be constrained by the normal legal protections. (IMO we in the USA need much stronger laws in re privacy protections, but that’s not your subject here, is it?)
It is simply a bad idea.
This initiative, if it somehow comes to fruition, is by its own nature a danger. Claiming that this will somehow increase security for those that already do not care is foolish (read the false sense of security part). All this does is off load blame for wrong doing away from end-users and service providers.
Don”t even think for a minute that the government wouldn’t become culpable for security and access issues in the eyes of the non-tech savvy.
Oh and corporations have a hard enough time with data leaks already. Plus, the government is atrocious in its record of IT projects. For reference, research the Bush administration trying to upgrade its internal e-mail service at the White House or perhaps the current issues regarding the near collapse of the information systems responsible for Social Security.
…and they plan to let people use this type of security on Windows?
JD,
I have a few points of contention to your article. In my mind, the single point of access is not an issue for 90% of internet consumers. I think it’s naive to think that the majority of consumers are using different passwords for all of their financial accounts (bank, PayPal, sites with stored CC#, etc) today. Those people already suffer from a single point of access. As for the tech savvy crowd? So long as the government does not _require_ the use of their internet id system, then it won’t change the way we do things.
Further, while having a single interface to financial data increases the risk of breach, it also increases the accountability of transactions. This, if done correctly, could streamline enforcement actions against hackers/scammers/etc.
Also, I’d have to imagine that in order for an institution (eCommerce site, bank, etc) to connect to the requisite national id API, there would be some vetting process, and a set of standards to which the institution would be held (e.g. levels of encryption, allowable stored user data, security and auditing). As it stands today, fear of lawsuits and bad press is the only thing keeping eCommerce companies “honest”.
Finally, the “big brother” factor already exists. The IRS can demand full disclosure of our financial transactions at any time they please. The credit reporting agencies have access to every one of our account numbers and account histories. Our information is already in the hands of juggernauts like PayPal and Bank of America. I don’t think that “big brother” knowing our username and password provides a significantly higher level of intrusion.
I’d like to close by saying again that my remarks are in regard to the use of the internet by neophytes, and not the tech savvy sort. Those are the people that really do need help securing their identity on the internet. It comes down to this question: Who do you trust more to protect them? A hodge-podge of blindly entrusted corporations, or the US Government. (And no, I’m not happy with either answer).
>When it comes to the Internet, the US government usually doesn’t have a clue.
According to who? With all due respect, for all its incompetencies and bureaucracy, the US Government and its various agencies and contracted efforts have repeatedly lead the world in science in engineering, to include having created the internet to begin with.
You make some legitimate points, but demand for responsible commerce and behavior dictates the need for some authentication mechanisms. This has been predicted as inevitable by computer scientists for decades.
There are plenty of quite legitimate concerns; you’ve cited many. Ultimately I don’t think an ID system need be entirely pervasive – information remains free and anonymous to the extent that certain publishers (anyone, really) choose to publish it that way. In cases where it makes sense to verify an identity (which is already the case to conduct business/commerce), it makes *more* sense from a consumer’s perspective to have one standard that is deemed “as reliable as possible” even if that’s a fallacy (even yet, one unreliable standard is better than a dozen unreliable standards).
The federal government didn’t actually do most of the work to create the Internet. Most of it was done by university and corporate lab researchers working under federal grants. The Department of Defense has always outsourced most of that work to skilled talent outside the federal government because that’s cheaper than running the equivalent of a UC Berkeley, MIT or Bell Labs in house.
More practically, though, the problem here is not engineering, it’s bureaucracy. The federal government does not have the institutional flexibility to operate a system like this. If you want a comparison, look at the Google identity system and Facebook Connect. The federal government doesn’t have the kind of payroll, personnel and property flexibility needed to hire the right minds, let them operate in the environment they need and “just get the job done” with regard to procurement.
If you look at most large federal information systems worked on in the last decade or so, they’re terrible failures compared to the private sector for those reasons.
I knew he was a commie, freaking Obama. But it doesn’t come as a shock as I suspected Obama of being the anti-christ
Sounds like something the anti-christ or his puppet would institute. All kidding aside it sounds worse than what Orwell imagined
Great article… and you nailed it.
This is all about controlling data and information. The U.S Government is realizing that it needs to control all this information, to be able to use it against the people.
We already have Ip addresses that can be tracked via your Internet Provider, you post something online and your IP address gets logged and can be back tracked to your computer. Even if your smart enough to use something as Tor people can find your original IP.
Seriously articles like this are to install fear in stupid computer users.
CNN is basically the Defense Department’s mouthpeice. Notice whenever there is a conflict (like the Georgia/Russia skirmish on 8.8.08) CNN always has the first word.
From your comments, you clearly haven’t read the National Strategy for Trusted Identities in Cyberspace. The US government isn’t proposing a single ID for cyberspace, nor anything like it.
I shouldnt be so shocked that there are comments in here defending this idea. You morons bent over and willingly showed the government where they could stick their throbbing rod on illegal wire-tapping, torture, illegal wars, airport x-rays and now you are going to do it again with this crap. Dont even respond to this comment because I wont be reading it. I am absolutely disgusted with people like you since you make it so easy for them to screw us over. There is not a single thread of legislation that needs to be added to the internet, its fine how it is and if you are stupid enough to get scammed stay away from it. Keep the government away from the internet as much as possible you stupid apes, its the last form of free communication we have and you are busting down the doors trying to give it away!
Bottom line, they know what they’re doing.
Is it a bad idea for us? YES. Great idea for them.
If this guy gets elected for a 2nd term then I will have officially lost all faith in the US populous’ ability to think freely.
Please google the following:
Define:DARPA
I stopped reading because it sounded like partisan drivel. AKA first paragraph.
sign of the apocalypse
I was thinking the same thing – one monetary system
Hahahaha – you get what you pay for. As long as america keeps putting up with stuff like this it will keep happening. Someday, people will wakeup and find they have the government they always wanted – and can’t stand it.
The bottom line is that the government can’t do anything better than the free market. They always take longer, refuse outside input, and spend a fortune building their broken products.
CNN is liberal?
I guess if you call constant stupid shots of you tube, news on something trivial as a animal showing up in a community and annoying one liners is liberal then ok. that being said, they dont realy take sides as i watch them to try and get a balanced view.
I have my issues with CNN, taking a partisan approach is not one of them.
“The Republicans should (hopefully) block any legislation from happening. This is where it is important to remain vigilant in protecting civil rights even in times where it seems that they allow for bad things to happen”
Then the Patriot Act should have been blocked.
Why did none of you Republicans bitch when G.W. Bush tried to implement the National ID system, for everyone, in the real world? The Democrats have blocked the “national ID” since they got in.
This implementation is meant to be for secure online transactions(commerce department), but will fail, just like Microsofts dot Net ID system, or any other online company that has tried a “one ID” system.
The biggest and most telling of these is Social Security ID. Social Security numbers were created for only one reason – to keep track of your contributions and how much you’re owed by Social Security.
Now, you’re required to give it to go to a bank, go to school, get a job, get a credit card, etc. etc.
What will happen is that businesses will say “this is the best way to protect ourselves” and if the majority of people adopt it, they will just refuse to do business with anyone that doesn’t use it. It becomes a slippery slope thing. It is unquestionably better for businesses, as it starts to put others on the hook for their security issues, so they will be clamoring to force all their customers to use it. The more people that do, the easier it will be to justify the decision. The more businesses that do it, the easier it will be for other businesses to do the same. Eventually, no major online retailer will do business without it.
It’s insanely important for people to resist this and to stay away from it. There are countless other reasons to not use it, but resisting it now is even more important as it’s become obvious that most people don’t think of the long-term ramifications of this decision and just say “Hey it makes it easier, and they say it’s safer, so why not?” The masses will gobble it up, and the people who are outliers will be stuck.
im not a high tech computer person, but the more i read out here the more convinced I am that this NSTIC is like a one on one tracking device. how do we resist it?
Weren’t the body scanners at the airports opt-in (e.g. you have the right to refuse?). I could easily see this going the same way…
“Sure you don’t have to have a national ID, but if you want to get on the internet you have to go down to the DMV, show 6 points of identification, obtain your temporary, & disposable passphrase, and then activate the 4 hour e-commerce access in the next 15 minutes…. Or you could opt-in.”
“A fine is a criminal sanction. A civil sanction, by contrast, is called a penalty. The term fine is sometimes used to describe a penalty, but the terms fine and penalty should be kept separate because the consequences are different: nonpayment of a criminal fine can result in incarceration, whereas nonpayment of a civil penalty cannot.”
I think you mean Civil Penalty , and not a Fine.
It’ll be hacked in 30 seconds and then the guberment will just spy on average citizens. FACT
It’s true. The Government already has the capacity to access any and all information about personal computer users. All this would do (and that’s not even for sure) is that accessing that data would become easier.
At the end of the day this is really more for the government to track my illegal activity’s and downloads.
You People dont have clue of what your talking about!! This is a great idea….. If the system is done properly it can resolve alot of problems. Taking into account my company owns the interlectual property for the application the presidents proposing. FYI we at perry security have the software to implement this system without failure.
People do speculate on almost everything that relates to Obama. And now here’s some speculation on the national ID! We all feel bad when government has access to all our info. Now that’s ridiculous.
Yes, thats what we all want to do. Poke in someone’s life. This is what we have done till now. Government is doing nothing but imitating us and giving us our own lessons.
Do I really need to tell that why government does all this? It is for our benefits and to stop any sort of bad things happening all around.
Safety is something we need to install in our lives. Government helps us in this way by scanning everything. It is its basic right.
How much more speculations and how many more news?
The only thing that Mr. Transparency wants is our personal lives to be transparent to the Government…Exactly what he criticized the Bush administration for…Oh, remember the Patriot Act that was so evil and to be abandoned? Well, not only did they keep it, they are going for this, Medical records, and much much more…kiss the “land of the free” farewell…that boat left on 10-1-2001.