In the digital age, where passwords are the virtual keys to your “house” or “safe” (or whatever metaphor you use), it’s important to have as many layers of protection as you can between bad actors and your digital assets. This is where two-factor authentication (or 2FA) comes into play.
What is two-factor authentication and why do I need it?
Two-factor authentication acts as an extra layer of protection and security. If your password is the key to your house, two-factor is the scary guard dog behind the door that will either welcome you home or be ready to prevent intruders from entering.
Using it is easy, though it does feel inconvenient at first since it requires an extra step in the login process. But requiring a double login means a hacker has to have access to multiple devices or accounts.
Once you install it, it will often ask you to press a button on another device or enter a unique code generated by your authentication app. While you might find it irritating or tedious, the payoff comes when you find multiple login attempts on your personal Facebook or Twitter rejected from a foreign IP address with your account protected by 2FA.
While hackers can get passwords from any of the hundreds of hacks and data breaches that have occurred over the last decade, they are still locked out of accounts with 2FA because they don’t have the unique authentication code needed to complete the login.
If you’re on Facebook, Twitter, Discord, etc. you should have the option of attaching a two-factor authentication method to your account. You can often find it by navigating into the settings and looking under the security tab of your favorite website. Most major websites now support the feature.
Find out if your favorite site has two-factor authentication by checking this list.
How secure is two-factor authentication?
In 2011, Gabe Newell, the CEO of Steam, gave away his Steam username and password to the public and openly challenged the audience and the Internet to gain access to his account. It’s been over 8 years since the challenge and no one has claimed victory.
The goal of the stunt was to demonstrate the effectiveness of Steam Guard, which emails you a code to complete the login process to Steam Gaming.
If the biggest name in PC gaming can openly trust two-factor authentication, it’s safe to say your account is pretty secure.
Types of two-factor authentication
Different sites offer different types of authentication methods. The most common types of two-factor authentication are:
- App-based authenticators (Facebook, Discord)
- Codes sent to your email address (Epic Games, Steam Guard)
- Codes sent to your cell phone number via SMS (Sony’s PlayStation Network, Gmail)
- A security key (Gmail, Facebook, Twitter, and more)
Using an authenticator app
First and foremost, you need an authenticator app. I personally have been using Authy for over 2 years. It is a free app on iOS and Android that offers the following features:
- All of your authenticator-bound accounts in one place;
- Cloud storage that allows you to access all of your accounts with your phone number to log in to the app;
- Use your fingerprint sensor to lock the app.
Activating two-factor authentication is easy once your authenticator app is installed on your trusted phone and computer.
- Visit the site you wish to activate two-factor authentication on and look for the option under security in the settings page.
- From there, you might be prompted to scan the QR code from your authenticator app. Simply open your authenticator app and do so.
- After scanning, you will have to enter the code that is displayed on your authenticator app into the box to confirm the sync between your app and the website.
- And you’re done!
For SMS-based authentication

- All you have to do is enter your area code and phone number when prompted.
- You will receive an initial text with a random code. You normally have 5 minutes to use the code before you need to issue a new one.
- Enter that code into the box and the process will be complete.
- Any time you want to log in to that website, you will get an SMS to your phone number. Make sure you are in a place that is getting reception/cell signals to ensure you get your SMS.
For email-based authentication

- The website will send an email with a unique code to your attached email address.
- Wait for the email which will have a unique code in it.
- Enter the code in the box when prompted to complete the setup.
Using a security key
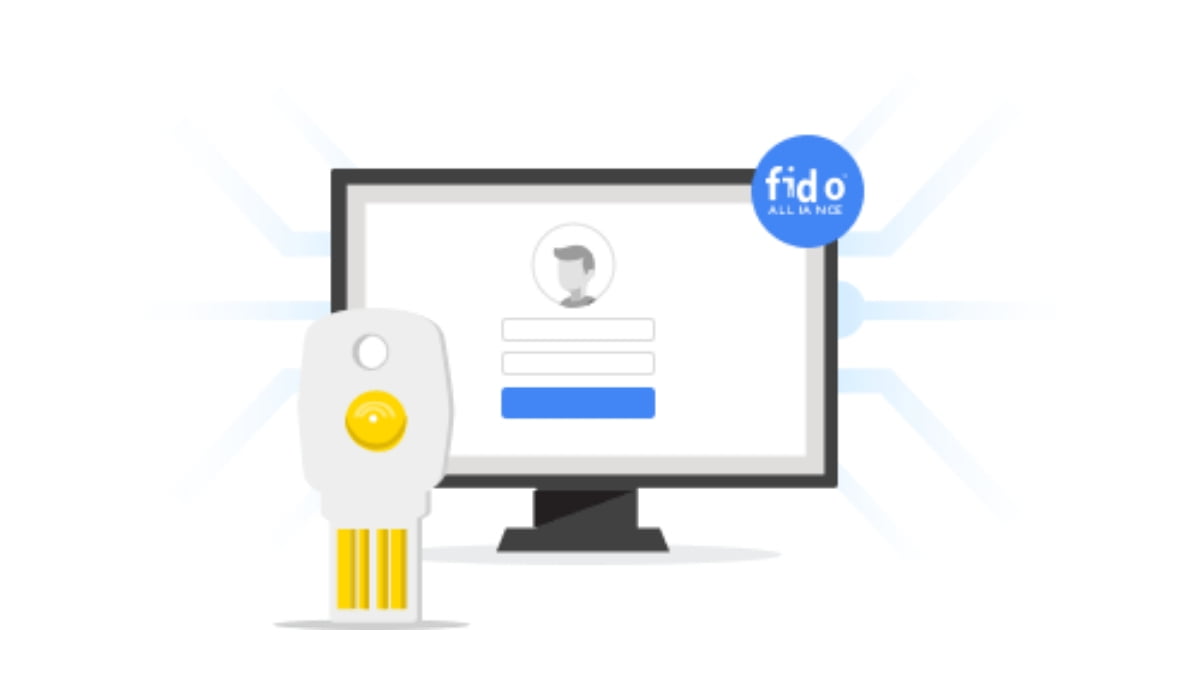
This is the most labor-intensive protection option. This method of security is most commonly used by celebrities, politicians, high-profile journalists, etc. If you are handling information or data that is essentially worth millions or can influence the stock of your company, then this is the way to go. If you just want to protect your selfies or unpublished cat albums, you’re better off with the other measures.
Here is a list of websites that currently support this form of a login and the video below show’s how it’s used.
The best key you can use for this is Google Titan. It costs $49.99 through the Google store and you can activate it by following the simple steps outlined on Google’s 2-step website.
All you have to do is follow the prompts on the website when you have the Titan key in your hand and you’re all set. Keep in mind, you need a key on you any time you want to log in. (We recommend keeping the Bluetooth key with you at all times as it works with laptops AND smartphones.)
I personally recommend activating two-factor authentication on EVERYTHING you can. Every single online identity of mine has a form of 2FA activated on it. You should take an hour to completely set up and protect all of your virtual online identities. An hour spent today saves you hours and sometimes days of phone calls, dealing with customer support, and other headaches you’d otherwise deal with if your account gets compromised.





Share Your Thoughts